Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
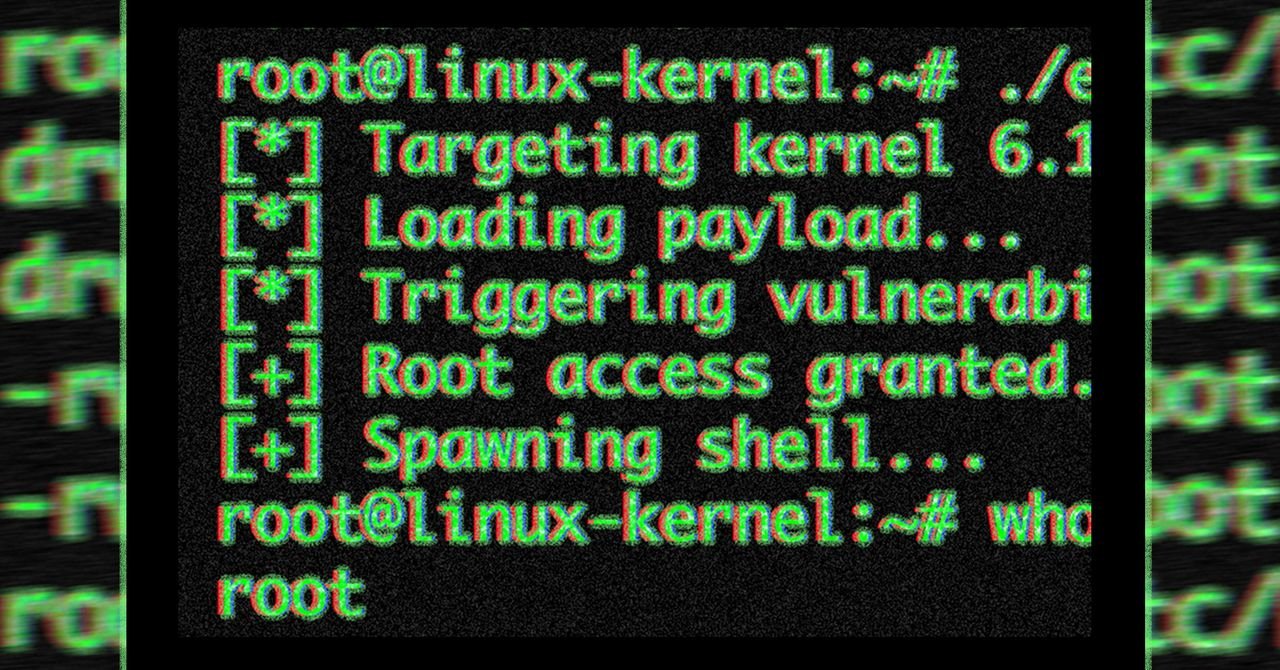
Publicly released an undetectable vulnerability code that provides access to almost all Linux distributions and sets off alarm bells as security guards rush to prevent massive intrusions inside the data center and on your devices.
Vulnerability is the use of code that uses these tools was released on Wednesday evening by researchers from the security firm Theori, five weeks after it was leaked to the Linux kernel security team. The group put the threat in the conversion 7.0, 6.19.12, 6.18.126.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254) but few of the Linux distributions included those fixes at the time the service was released.
The main flaw, listed as CVE-2026-31431 and named CopyFail, is local privilege escalation, a type of vulnerability that allows unprivileged users to elevate themselves to administrators. CopyFail is particularly dangerous because it can be exploited by a single exploit – released on Wednesday – which works by distributing all of the vulnerable data without modification. With this, an attacker can, among other things, break into multi-tenant systems, break out of containers based on Kubernetes or other systems, and create malicious requests that call exploit code. CI/CD work in progress.
“‘Regional opportunity growth’ sounds dry, so let me strip it down,” researcher Jorijn Schrijvershof he wrote on Thursday. “It means: An attacker who already has access to the system, even if it’s a user without boring access, can upload himself. From there he can read any file, install backdoors, inspect any process, and change other systems.”
Schrijvershof added that the same Python script Theori released works reliably for Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12. The researcher continued:
Why is it important to share groups? Because “local” has a lot of space in 2026: every container on a Kubernetes node, every tenant on a shared box, every CI/CD application that has an untrusted application code, every WSL2 instance on a Windows laptop, every AI agent is given a shell. They all share the same Linux kernel with their neighbors. The kernel’s LPE will break that limit.
The real threat looks like this. The attacker uses a well-known WordPress plugin vulnerability and obtains shells such as www-data. They run a copy.fail PoC. They are now rooted in the crowd. Any other lender can be found suddenly, which is how I went through the dead end. Vulnerability does not allow the attacker to enter the box; it changes what happens in the next ten seconds when it reaches that point.
The vulnerability stems from a “straight line” bug in the kernel’s crypto API. More information to use color conditions and memory corruption errors do not work well in kernel configurations or partitions, and sometimes even on the same machine. Because the published code of CopyFail uses logical errors, “reliability is not possible, and the same documents work for distribution, researchers from Bugcrowd. he wrote. “No running window, no kernel offset.”
CopyFail gets its name because the Authencesn AEAD template method (used as IPsec sequence numbers) does not copy data when it should. Instead, it “uses the caller’s destination as a pointer, writes 4 bytes across the valid region, and doesn’t return it,” Theori said. “A ‘copy’ of AAD ESN bytes ‘fails’ to be within the destination buffer.”
Some security experts also pointed out that CopyFail is a serious vulnerability, and one to say is “the worst kernel vulnerability in recent memory.”
The latest Linux vulnerability was The Black Pipe from 2022 and Black Cow in 2016. All these weaknesses were used quickly in the wild.